Example: Cyber/Operational Security
This is a story I composed for our weekly newsletter Three Things. We included it across multiple channels after IT asked for help to get help employees at the USO understand the stakes of operational and cyber security and engage in the tools to enhance behaviors. As an organization that is stationed abroad alongside our service members, these communications are in important part of ensuring safety and the integrity of our relationship with the Pentagon. My objectives were to make it interesting, using the strength of our historical brand, and provide easily memorable tips and clear calls-to action to engage with more resources.

In Modern War, OPSEC Matters Even More
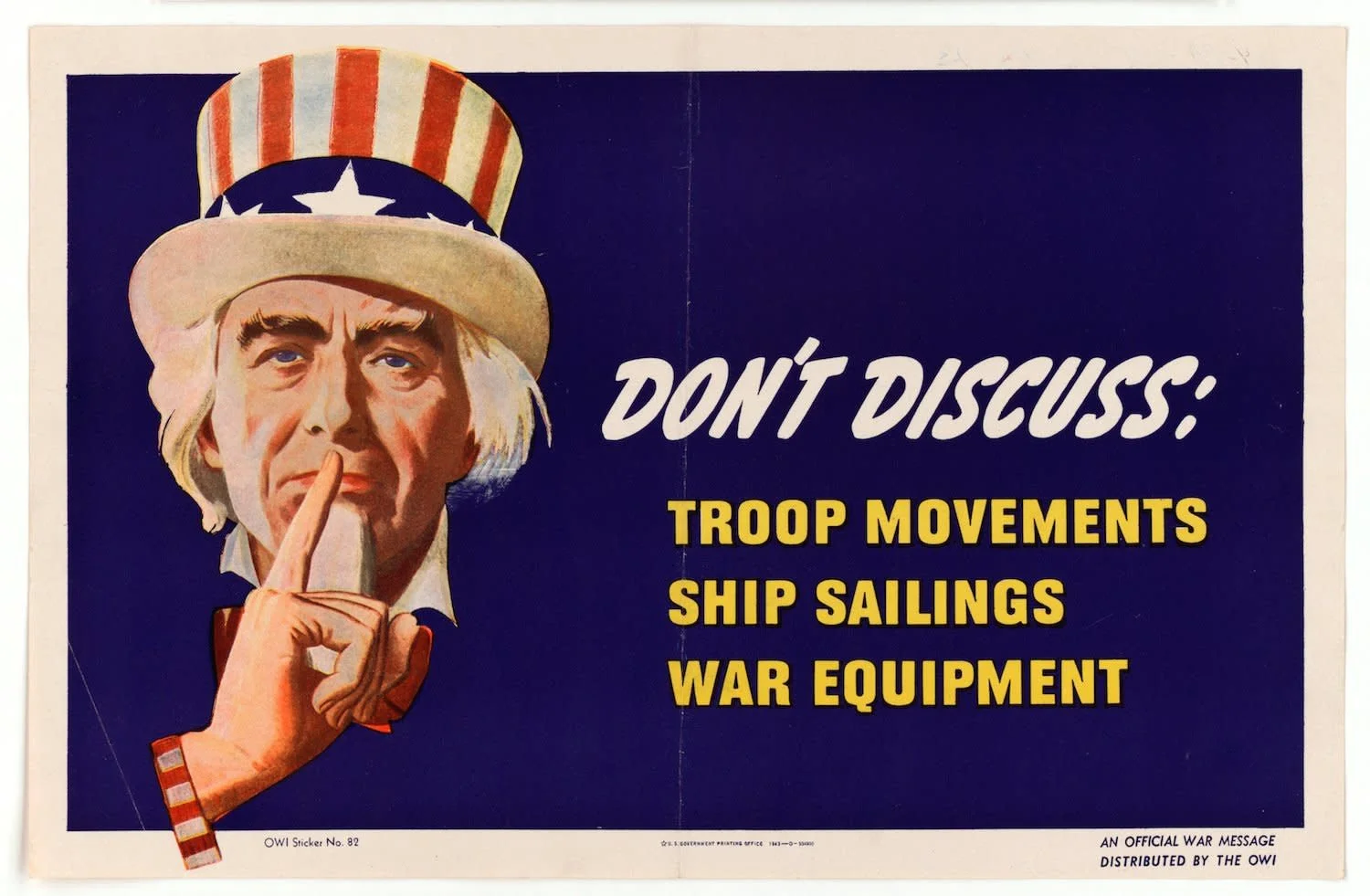
Operational Security (OPSEC) is the processes and norms our society uses to protect critical information that can harm Americans. We say “society” instead of the military because every citizen has a role to play in the information age.
The USO has prioritized OPSEC since our inception. Just check out this fascinating example from a 1944 guide for USO staff, provided by our archivist and USO historical guru Mike Case:
USO Camp Shows: A Guide to the Foxhole Circuit, 1944, from the USO Archives
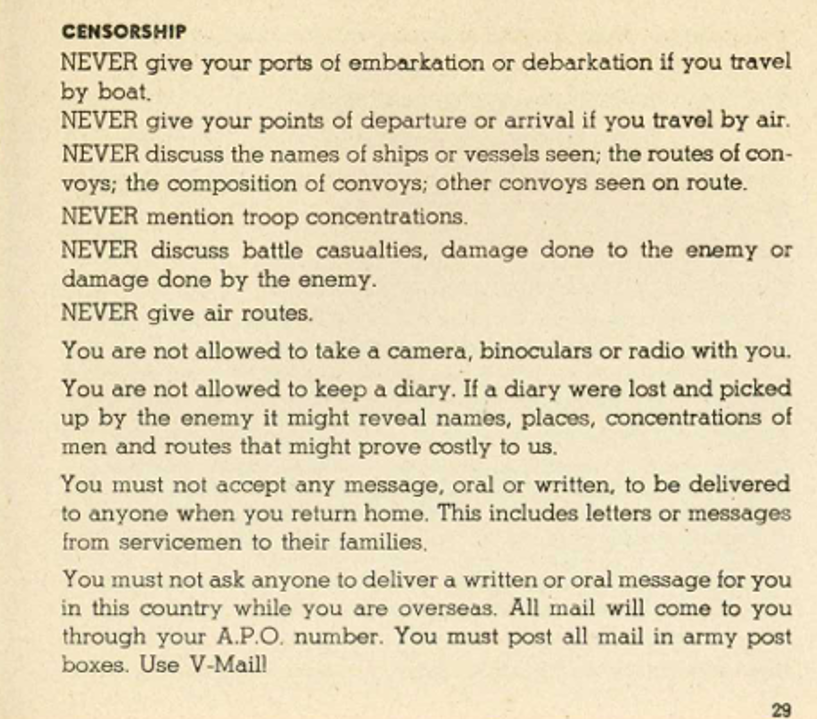
The mention of a diary is quaint but it also foreshadowed the complications of the social media age, just one of many factors driving the need for all Americans to practice better OPSEC today:
The threat is constant, regardless of whether we are officially at war or not. From rival nations to regional threats and sophisticated terror groups or just a lone wolf, in a world of "forever wars" there are numerous factions constantly seeking information to do us harm.
Open Source Intelligence (OSINT) gives our enemies more capability than ever. OSINT is when regular people use openly available sources like social media, satellite images and news sites to accurately analyze a situation, often better than some professional intelligence agencies could, even just 10 years ago. Now they are using AI. Some of these people are hostile to the US, or would be...for the right price. Don't let your geo-located pic on Instagram be the final piece of a puzzle our enemies need.
The threat is increasingly personal. Of course we always want to protect our servicemembers, but we are personally more at risk too. Bad OPSEC in the information age is riskier, and American hostages are more valuable to our enemies than ever.
When in doubt, just don't say it or post it. If you are not absolutely sure you won't harm OPSEC by disclosing something, don't post that picture, don't tell people you are evacuating. Don't do anything. Get guidance first. Err on the side of caution.
Rank is not always right. If a supervisor tells you to post or say something you feel could be bad OPSEC, don't do it. Have a conversation. If you can't resolve it without still feeling like there is risk, take it to the next level. An annoyed supervisor is temporary. Living with an OPSEC failure will be lifelong.
Be an expert on security basics, and never stop learning. Since most of us do not have permission to speak with the media, the biggest threats are digital and travel security. Check out these resources below, and thanks to Kelly Lane, from our training department for sourcing all of them!
Three Things to Remember for Better OPSEC

